Secure by Design. Trusted by Enterprise.
Security is built into every layer of Qinfinite. From infrastructure isolation to AI governance, your data, systems, and operations remain secure, controlled, and fully auditable at all times.
Built on Principles, Not Just Controls
-
Zero Trust Access
Every access request is verified, authenticated, and audited using strict role-based controls and multi-factor authentication at every layer. -
Complete Customer Isolation
Each customer operates in a fully isolated environment with no shared compute, network, or data layers, ensuring complete independence and security. -
Continuous Visibility
All actions, changes, and interactions are continuously monitored and logged to ensure full traceability and accountability. -
Adaptive Security
Security evolves with your infrastructure, automatically adapting to new systems, services, and dependencies as they change.

How Qinfinite Secures Your Environment
From Access Control to End-to-End Protection
Qinfinite embeds security across every layer of the platform by enforcing strict access controls, protecting sensitive data, and continuously monitoring system activity to ensure complete visibility, control, and resilience across your enterprise environment.
01
Controlled Access
Centralized, least-privilege access model with no standing access and fully audited sessions.
02
Secrets Protection
Credentials are dynamically generated, securely stored, and continuously rotated to prevent misuse.
03
Network Security
Strict inbound and outbound controls ensure only trusted and verified traffic is allowed.
04
Full Observability
Every system activity is logged, monitored, and traceable for complete auditability.
05
AI & Automation Enablement
Feed contextual intelligence into Agentic AI workflows, automation engines, and operational insights.
Key Benefits
Responsible AI
for Enterprise Operations
Qinfinite ensures AI operates with full transparency, governance, and contextual awareness, enabling intelligent decisions that remain controlled, explainable, and aligned with enterprise policies.
Benefit 01
Transparent Decisions
AI recommendations are based on system context and are fully explainable.
Benefit 02
Human Control
Critical actions follow approval workflows to ensure human oversight.
Benefit 03
Policy-Driven Automation
All automation aligns with defined enterprise security and compliance policies.
Benefit 04
Context-Aware Intelligence
AI understands system relationships to enable safer and more accurate decisions.
Enterprise-Grade
Compliance and Resilience
Security that is continuously validated, audit-ready, and built to respond with control and precision.

Compliance by Design
Structured Incident Response

Proactive Risk Management
A strategic perspective on how leading enterprises are building intelligent IT operations.
Download our point of view (POV)
Exceptional outcomes driven by Agentic AI
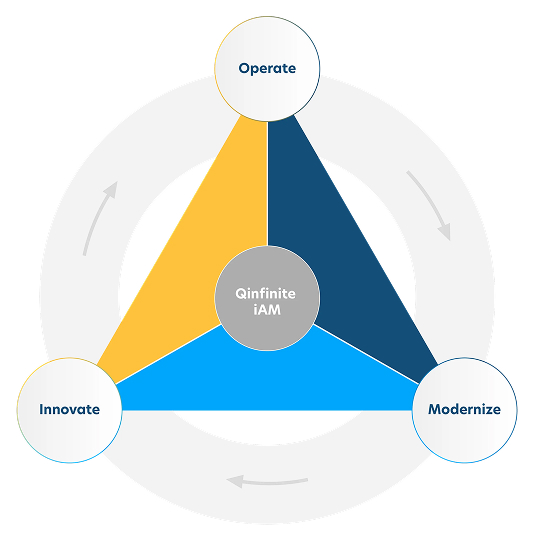
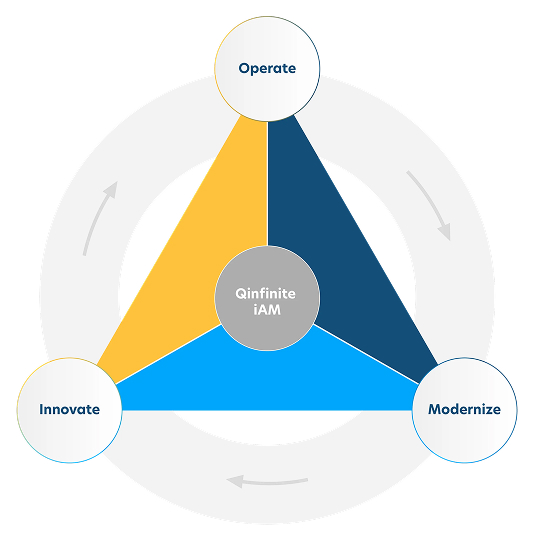
Why Qinfinite
Security That Works Across
Your Entire IT Landscape
What makes Qinfinite different is not just how it secures systems but how it connects security with operations and intelligence.
By combining:
- Real-time system understanding
- Cross-domain visibility
- Intelligent, policy-driven workflows
Qinfinite enables a security model where risks are understood in context, decisions are made faster and actions are consistent and governed.
What This Means for Forward Looking
Enterprises Like You
With Qinfinite, you don’t just get a secure platform, you build enterprise trust and credibility. This could mean
- Complete control over your environment
- Full visibility into every action and change
- Stronger compliance posture without added complexity
- Safer AI-driven operations with governance built in
- Reduced risk exposure across your IT ecosystem
Every Qinfinite customer operates in a fully isolated environment with no shared compute, network, or data layers. This means your data is never co-mingled, your infrastructure is dedicated, and your environment is completely independent. This architecture eliminates cross-tenant risk by design.
Access to customer environments is tightly controlled through centralized identity management, multi-factor authentication (MFA), and role-based, least-privilege access. Every session is fully audited and time-bound. There is no unmanaged or standing access, ensuring complete control and traceability.
Qinfinite uses secure, vault-based mechanisms with dynamically generated, short-lived credentials and regular rotation and audit of access keys. There are no hardcoded or exposed secrets in the environment. Even if credentials are compromised, they cannot be reused.
Qinfinite environments are protected through multiple layers, including application-level protection against common attacks like injection or bot traffic and network-level controls that allow only trusted and approved access. The system maintains continuous monitoring of traffic and behavior to ensure security. Only trusted and verified access is allowed.
Yes. Every action across the platform is logged, monitored, and audited. This includes user access, infrastructure changes, and system-level activity. This ensures complete transparency and accountability.
Qinfinite follows a structured, SOC 2-aligned incident response process that involves detecting and identifying issues in real time before containing and isolating impacted systems. The process continues by eradicating threats, recovering to restore services safely, and notifying stakeholders to communicate transparently. This ensures a fast, controlled, and reliable response.
Yes. Qinfinite follows SOC 2 Type II-aligned practices, including access control, auditability, and continuous monitoring. The platform performs regular security and compliance checks along with consistent reviews and assessments.
Qinfinite’s AI is designed to be safe, governed, and transparent through human-in-the-loop controls for critical actions and policy-driven automation that prevents uncontrolled execution. The system makes context-aware decisions using system relationships to ensure there is no black-box behavior. AI enhances operations without compromising control.
No direct or unrestricted access exists. All access requires authorization, is logged and audited, and is limited to specific, approved scenarios. You maintain full control over your environment and data.
Security is continuously enforced through ongoing monitoring, anomaly detection, and automated security checks in development pipelines. The platform also undergoes regular vulnerability assessments and testing. Security adapts continuously as your environment evolves.
Measurement & Insights
Security and Trust Frequently Asked Questions
Ready to start?
Start your journey toward resilient, intelligent IT operations.