You Can’t Secure What You Can’t See.
Uncover hidden applications, unknown assets, and unmanaged systems across your enterprise.
Traditional tools often overlook the “shadow IT” landscape of unapproved SaaS and untracked infrastructure that creates significant visibility gaps.
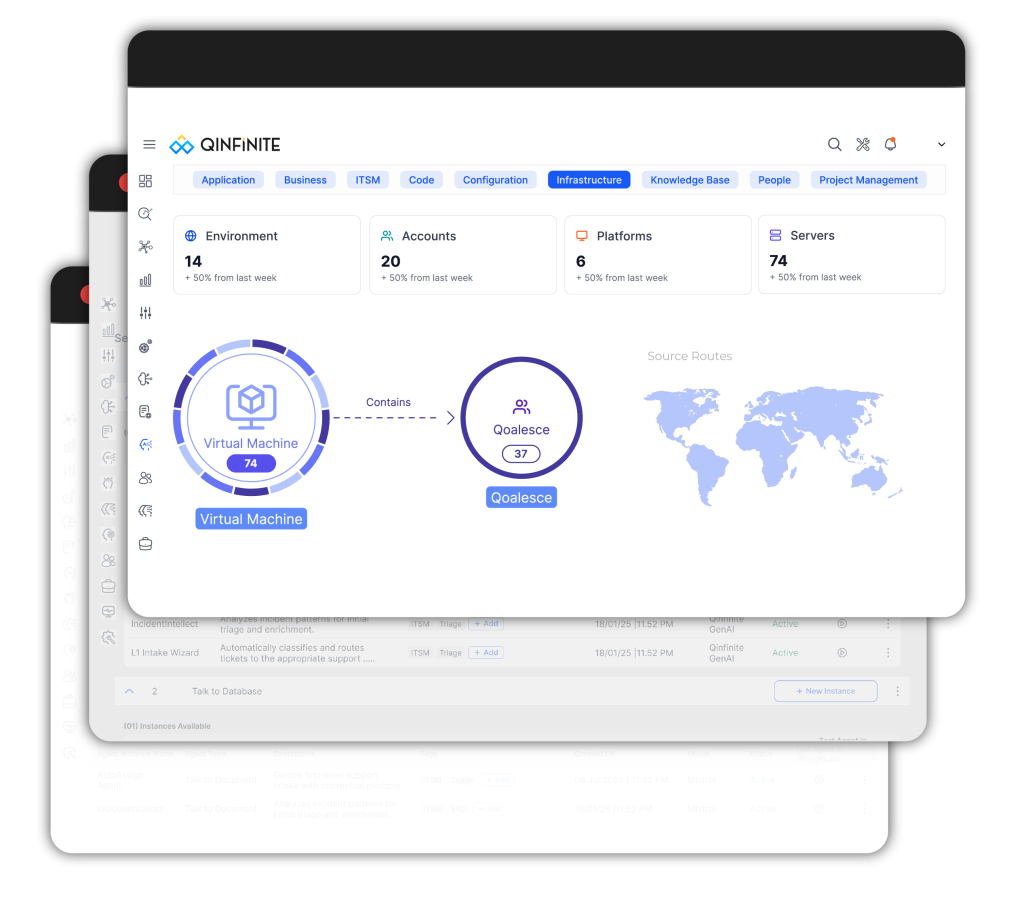
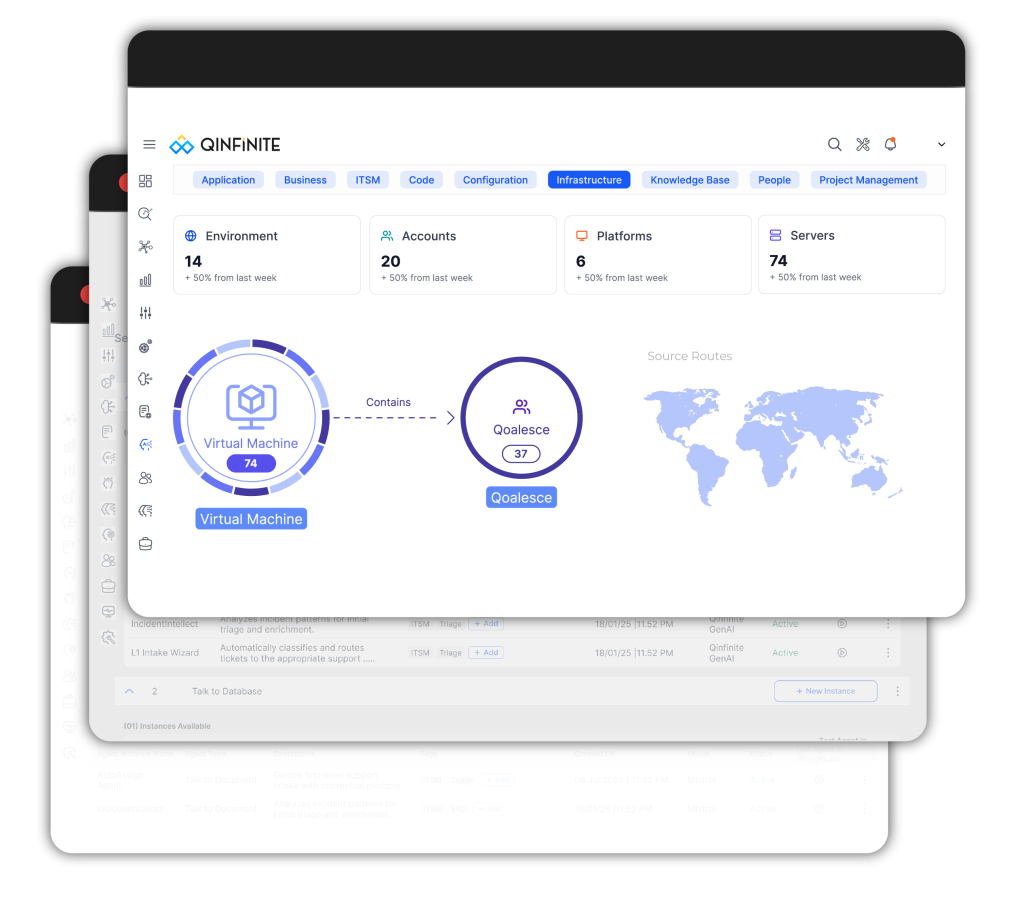
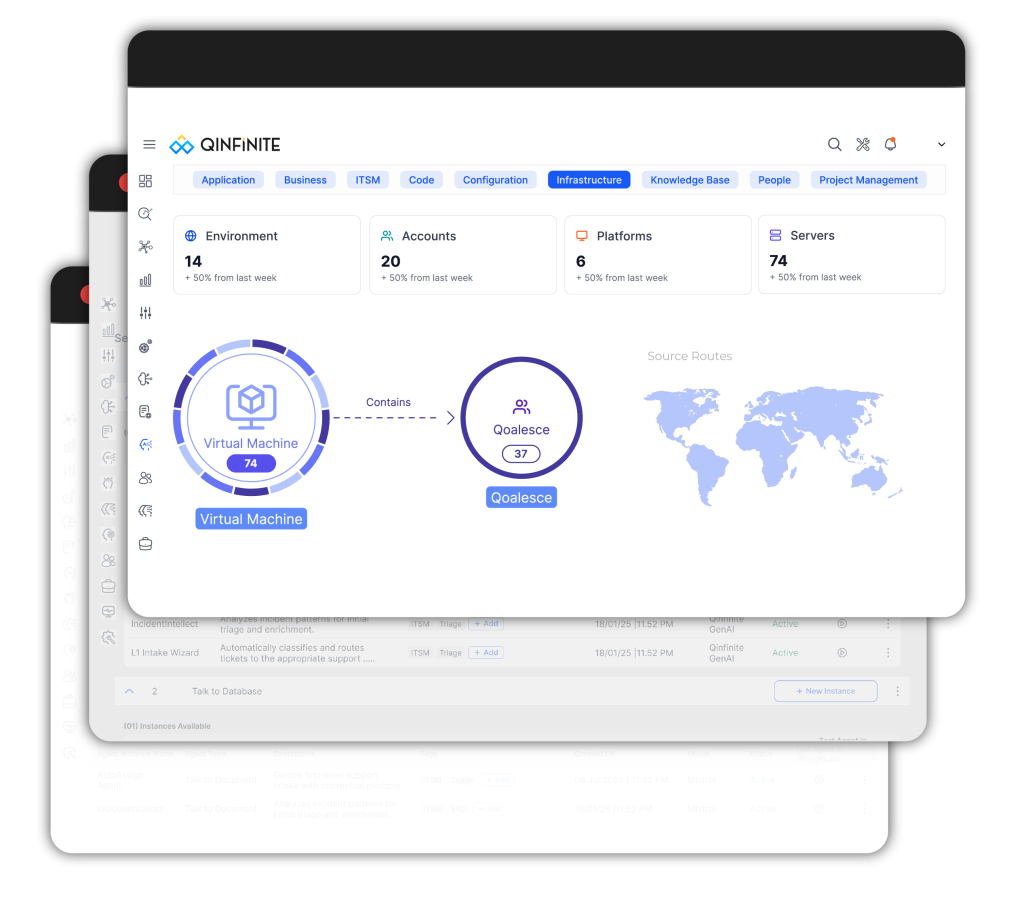
Qinfinite solves this by continuously discovering your entire IT environment and mapping the dependencies you didn’t know existed.
By providing this essential context and risk analysis, the platform ensures you can effectively secure, optimize, and govern every part of your enterprise.
Key Outcomes
- Discover unknown applications and shadow IT assets across environments
- Identify unauthorized SaaS usage and unmanaged systems
- Understand dependencies and business impact of hidden assets
- Take intelligent, policy-driven action to reduce risk and cost
Recognized in Forrester's "The AIOps Platforms Landscape"
Quinnox, a leading digital transformation partner leveraging advanced technology solutions, proudly announces its inclusion as one of the Top 25 Vendors in Forrester’s The AIOps Platforms Landscape, Q4 2024.
How Qinfinite Turns Shadow IT into Actionable Intelligence
From hidden assets to controlled environments – Qinfinite continuously discovers, maps, and governs your entire IT ecosystem in real time.
Shadow IT is not just about unknown applications, it’s about unknown relationships, risks, and costs.
Qinfinite continuously scans your environment, identifies unmanaged systems, and maps their connections to applications, infrastructure, and business services.
This transforms shadow IT from an invisible risk into a clearly understood and actionable part of your IT landscape.
01
Continuous Discovery of Unknown Assets
Automatically detect applications, SaaS tools, and infrastructure that exist outside formal governance.
02
SaaS & Application Visibility
Identify unauthorized or untracked SaaS usage across teams and departments.
03
Dependency & Context Mapping
Understand how shadow IT assets connect to your systems, data, and operations.
04
Risk & Impact Analysis
Evaluate the security, compliance, and operational impact of hidden assets.
05
Agentic AI–Driven Remediation
Trigger intelligent, policy-driven actions to govern, restrict, or eliminate shadow IT safely.
Key Benefits
Bring Visibility, Control, and Confidence
to Your IT Landscape
Complete IT Visibility
Discover and track all applications, services, and infrastructure—including hidden and unauthorized assets.
Reduced Security Risk
Identify vulnerabilities and unauthorized access points before they become incidents.
Controlled SaaS & Cloud Spend
Eliminate redundant tools and reduce cost leakage from unmanaged usage.
Governed & Intelligent Operations
Enforce policies and automate actions to maintain control across your IT ecosystem.
Why Shadow IT Remains a Persistent Enterprise Risk

Invisible Applications & Assets

Unmanaged SaaS Sprawl

Unknown Dependencies & Risk Exposure
Stop Managing What You Know. Start Discovering What You Don’t.
Use Cases
Shadow IT Discovery Tailored to Your Enterprise Needs
Industry-Specific Shadow IT Visibility
Different industries face unique risks from shadow IT. Qinfinite helps uncover hidden systems while aligning with regulatory and operational requirements.
-
Financial Services
Detect unauthorized applications and ensure compliance with strict regulatory frameworks. -
Healthcare
Identify shadow systems that could expose sensitive patient data. -
Manufacturing
Uncover hidden IT and OT systems across distributed environments. -
Retail
Track unauthorized SaaS tools impacting customer data and operations.
Outcome-Driven Shadow IT Management
Transform shadow IT from an unknown risk into a managed, optimized, and controlled part of your enterprise.
-
Shadow IT Discovery & Inventory
Identify all unknown applications and infrastructure across your environment. -
SaaS Usage Optimization
Detect redundant or unused SaaS tools and reduce cost leakage. -
Security & Risk Management
Identify vulnerabilities and unauthorized access points. -
Compliance & Governance
Ensure all systems align with enterprise policies and regulatory standards.
Actionable Visibility for Every Stakeholder
Equip security, IT, and business leaders with the insights needed to identify, manage, and control shadow IT.
-
CIO / Head of IT
Gain full visibility into enterprise IT landscape and eliminate blind spots. -
CISO / Security Leaders
Identify and mitigate risks from unauthorized systems and applications. -
IT Operations Leaders
Ensure stability and control across known and unknown infrastructure. -
Finance / Procurement Leaders
Reduce SaaS sprawl and optimize technology spend.
Resources
Insights on Intelligent IT Operations